19
HANDS ON incident-responder
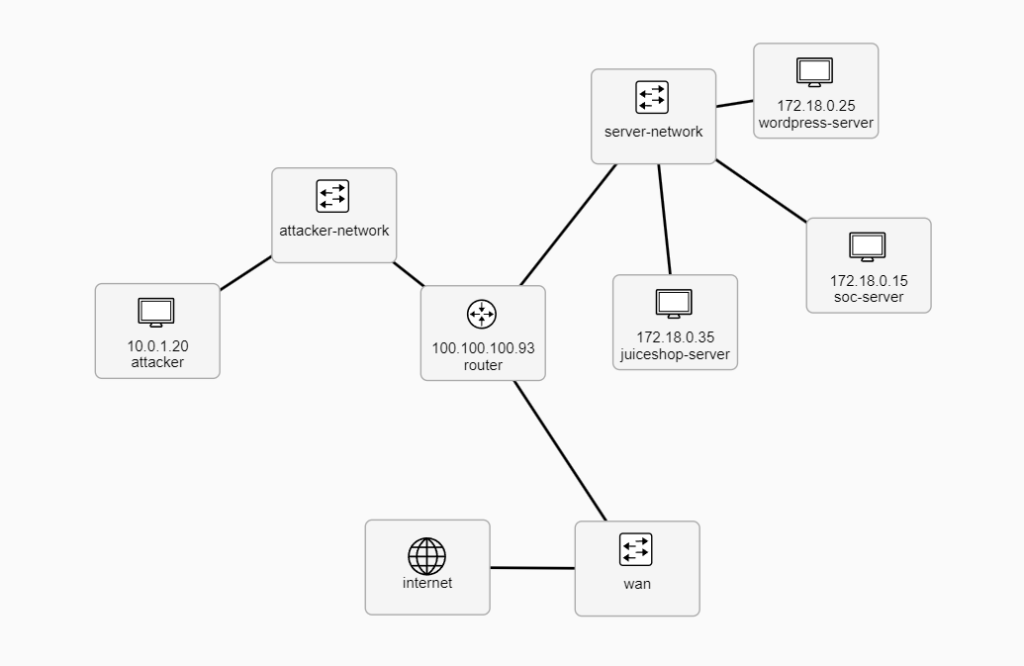
Your goal is to investigate attacks which were performed against two web servers, one is running WordPress and the other Juiceshop eshop. The attacks have already happened, but if needed you can run them again by logging in to attacker and running scripts simple-attack and advanced-attack stored in /usr/local/bin.
First, you can investigate the attacks in Kibana. Login to soc-server and login to https://kibana.ex:5601 with administrator:exercise.
Second, find the same attacks in suricata. Suricata is installed on both wordpress-server and juiceshop-server, so login to both with SSH from soc-server or with Open CLI from KYPO to use suricata with CLI.
Finally, investigate the RAM image with volatility. TODO
Sandbox access
- In the topology overview on, right-click on the machine you want to connect to and then click on
Open GUIorOpen CLI, and a new pop-up window will appear. - Login with username
userand passwordPassword123.
TOPOLOGY